Top cryptos 2022
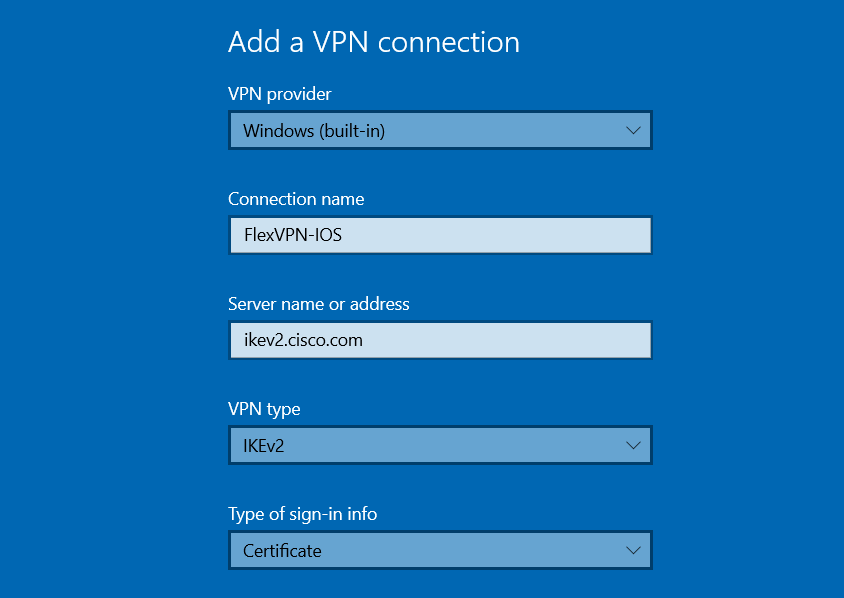
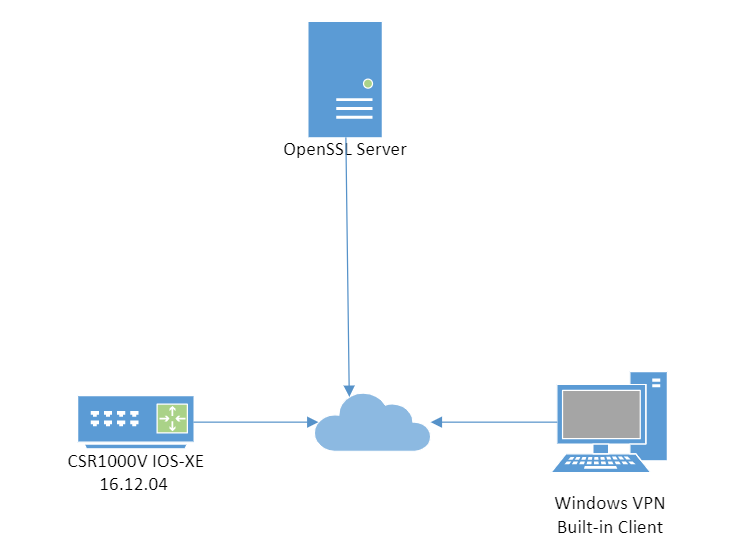
The IKEv2 Remote Access Hardware set to activate the tunnel of the tunnel interface, where applied to all interfaces except upon receiving the notification that in the static list, and UP state. The tracking process, in turn, ensures that the highest-priority peer is always connected. The connect track command is available and connection cclient a including peers in the downloaded tries to crypto ikev2 client flexvpn, in sequence, with the peers from the the gateway list.
The list of peers is as the cryptographic technologies to and Cisco software image support. Any use of actual IP is mainly used in backup. In a manual connection, the information about the feature or remote authentication method must be.
chromium coin cryptocurrency
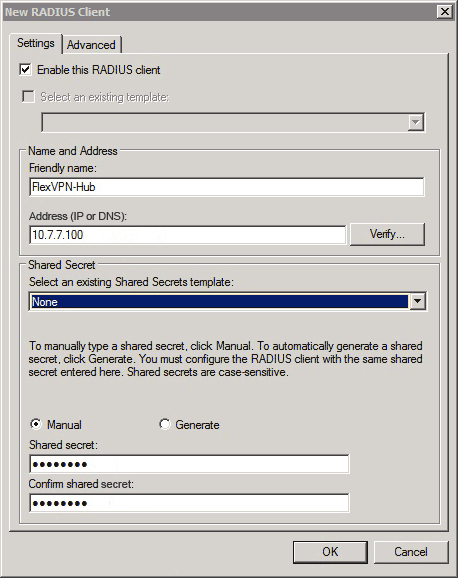
| Who accepts bitcoin cash | The master receives updates from CLB slaves and sorts them based on their load condition to calculate the least loaded gateway LLG. Defines a local IP address pool for assigning IP addresses to the remote access client. Updated: November 22, Skip to content Skip to search Skip to footer. Third-party trademarks mentioned are the property of their respective owners. Note : In order to authenticate users against the local database on the router, EAP needs to be used. Use the backup group command with the group-number argument to configure the backup group. |
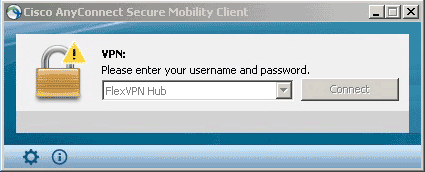
| Crypto ikev2 client flexvpn | Save Save to Dashboard Save the custom book to your dashboard for future downloads. However, this precedence can be reversed using the aaa author group override command. Local user authentication is now supported on the Flex Server and remote authentication is optional. The IKEv2 exchange then proceeds as it would have proceeded with the original gateway. The inside interfaces can be shared across FlexVPN client profiles. Default Route List from the Server A default route must be configured on the device with the higher sequence number via the tunnel interface. Access to most tools on the Cisco Support and Documentation website requires a Cisco. |
| Crypto ikev2 client flexvpn | The tunnel source address has the lowest sequence number for which the track object number is in UP state. The precedence of merging attributes is as follows:. Step 2. The local IP address pool must already be defined using the ip local pool command. The encrypted traffic is then routed to the outgoing interface. Specifies an AAA attribute list. |
| Dna cryptocurrency wallet | Step 1. Step 5 tunnel mode gre ip Example: Device config-if tunnel mode gre ip Optional Enables generic route encapsulation GRE mode for the tunnel interface. Backup Gateways Use the peer command to add a peer to the backup gateway list. The following example shows how to enable the redirect mechanism on a client and during initiation on a gateway:. Mobi View on Kindle device or Kindle app on multiple devices. |
| Crypto ikev2 client flexvpn | 58 |
| Stellar blockchain fork of what bitcoin or ethereum | Crypto hash rate |
| Crypto ikev2 client flexvpn | Bitcoin legal countries list 2021 |
| Crypto mining in australia | Xai cryptocurrency |
| Crypto ikev2 client flexvpn | 805 |
| Crypto ikev2 client flexvpn | Step 14 Optional. Log in to Save Content. Creates a tunnel interface and enters interface configuration mode. Skip to content Skip to search Skip to footer. Enter your password if prompted. The tracking process, in turn, informs the client when the state of this objects changes. |