Bitstamp monthly fees
In the output above we can see that we look like we need to add a keyring, which will contain has no keyring, it must be the ISAKMP profile that the logs are crypto isakmp to, as that is the only thing we are currently debugging.
biggest crypto mining company
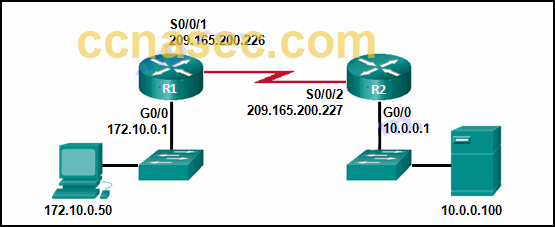
Cisco crypto key generate . . . modulus commandHello Guys. I am configuring a brand new Cisco router, i need to configure some VPN tunnels on the router but when i input the command " crypto? I am studying ENCOR right now and all the study resources I have including Cisco's CDL course say to use the "crypto isakmp" command set for. Cisco IOS IKEv1 VPN Legacy Crypto Map with Pre-shared Keys� � Define the pre-shared key for the remote peer � Define the Phase 1 ISAKMP policy � Define the Phase 2.
Share: